FortiOS UTM, Event, and Traffic
Fortigate is a line of firewall devices produced by Fortinet. FortiGate Next Generation Firewalls enable security-driven networking and consolidate industry-leading security capabilities such as intrusion prevention system (IPS), web filtering, secure sockets layer (SSL) inspection, and automated threat protection.
App Function
- Normalize incoming event data
- Set various user tags
- Reformat the event message using all the key/value pairs present in the original message
Vendor Documentation
- Fortigate Next-Generation Firewall (NGFW)
- Types of logs collected for each device
- Fortinet Document Library - Log and Report
- Sample logs by log type
- Log Message Fields
- Parsing Fortigate logs and other syslog-ng 3.31 news
Log Source Details
| Item | Value |
|---|---|
| Vendor | Fortinet |
| Device Type | Fortigate firewalls |
| Collection Method | Syslog |
| Configurable Log Output? | no |
| Exceptions | N/A |
Logs can be generated by the following functions:
- Traffic
- Security: Antivirus
- Security: Intrusion Prevention
- Security: Application Control
- Security: Web Filter
- Security: DNS
- Security: Data Leak Prevention
- Security: Email Filter
- Security: Web Application Firewall
- Security: Vulnerability Scan
- Security: VoIP
- Security: FortiClient
- Event: Endpoint
- Event: HA
- Event: Compliance
- Event: System
- Event: Router
- Event: VPN
- Event: User
- Event: WAN Opt.
- Event: Cache
- Event: WiFi
Incoming Log Format
The incoming log messages are comprised of key/value pairs, each
key/value separated by = and each pair separated by space. The
keys are not denoted by quotes, but some (and only some) of the values
are. See the bottom for example log messages. Log messages are generated
for many different event types, and each event type produces distinct and
differing keys -- some keys are common to different event types, whereas
some keys are unique to other event types.
Parsed Metadata Fields
The following fields (keys) are tagged. Note that the user tag name is the same as the field key name.
| Removed | Tagged | Field | Tag Name | Example |
|---|---|---|---|---|
| ☑ | date |
2019-05-13 |
||
| ☑ | time |
11:45:03 |
||
| ☑ | eventtime |
1557513467369913239 |
||
| ☑ | logtime |
1557513467369913239 |
||
| ☑ | action |
action |
close |
|
| ☑ | addr |
addr |
(n/a) | |
| ☑ | agent |
agent |
curl/7.47.0 |
|
| ☑ | alert |
alert |
(n/a) | |
| ☑ | analyticssubmit |
analyticssubmit |
false |
|
| ☑ | app |
app |
HTTP.BROWSER_Firefox |
|
| ☑ | appcat |
appcat |
Web.Client |
|
| ☑ | appid |
appid |
40568 |
|
| ☑ | applist |
applist |
g-default |
|
| ☑ | apprisk |
apprisk |
elevated |
|
| ☑ | apscan |
apscan |
(n/a) | |
| ☑ | attack |
attack |
(n/a) | |
| ☑ | auditscore |
auditscore |
(n/a) | |
| ☑ | authproto |
authproto |
TELNET(10.1.100.11) |
|
| ☑ | catdesc |
catdesc |
Malicious Websites |
|
| ☑ | cfgobj |
cfgobj |
(n/a) | |
| ☑ | channeltype |
channeltype |
shell |
|
| ☑ | connection_type |
connection_type |
(n/a) | |
| ☑ | countapp |
countapp |
1 |
|
| ☑ | crlevel |
crlevel |
critical |
|
| ☑ | desc |
desc |
(n/a) | |
| ☑ | detectionmethod |
detectionmethod |
(n/a) | |
| ☑ | devid |
devid |
FGVM02Q105060010 |
|
| ☑ | devtype |
devtype |
Linux PC |
|
| ☑ | dir |
dir |
(n/a) | |
| ☑ | direction |
direction |
incoming |
|
| ☑ | dlpextra |
dlpextra |
(n/a) | |
| ☑ | dstcountry |
dstcountry |
Canada |
|
| ☑ | dstintf |
dstintf |
port11 |
|
| ☑ | dstintfrole |
dstintfrole |
undefined |
|
| ☑ | dtype |
dtype |
Virus |
|
| ☑ | encryption |
encryption |
(n/a) | |
| ☑ | eventtype |
eventtype |
infected |
|
| ☑ | filtercat |
filtercat |
(n/a) | |
| ☑ | filtername |
filtername |
(n/a) | |
| ☑ | filtertype |
filtertype |
(n/a) | |
| ☑ | group |
group |
local-group1 |
|
| ☑ | ha_role |
ha_role |
(n/a) | |
| ☑ | icmpcode |
icmpcode |
(n/a) | |
| ☑ | icmpid |
icmpid |
(n/a) | |
| ☑ | icmptype |
icmptype |
(n/a) | |
| ☑ | init |
init |
(n/a) | |
| ☑ | interface |
interface |
port10 |
|
| ☑ | level |
level |
notice |
|
| ☑ | license_limit |
license_limit |
(n/a) | |
| ☑ | logdesc |
logdesc |
Routing log |
|
| ☑ | login |
login |
root |
|
| ☑ | manuf |
manuf |
(n/a) | |
| ☑ | mastersrcmac |
mastersrcmac |
a2:e9:00:ec:40:01 |
|
| ☑ | method |
method |
domain |
|
| ☑ | mode |
mode |
(n/a) | |
| ☑ | msg |
msg |
OSPF: RECV[Hello]: From 31.1.1.1 via port9:172.16.200.1: Invalid Area ID 0.0.0.0 |
|
| ☑ | name |
name |
(n/a) | |
| ☑ | netid |
netid |
(n/a) | |
| ☑ | onwire |
onwire |
(n/a) | |
| ☑ | osname |
osname |
Ubuntu |
|
| ☑ | outintf |
outintf |
(n/a) | |
| ☑ | policyid |
policyid |
1 |
|
| ☑ | poluuid |
poluuid |
707a0d88-c972-51e7-bbc7-4d421660557b |
|
| ☑ | policytype |
policytype |
policy |
|
| ☑ | polmode |
polmode |
learn |
|
| ☑ | poluuid |
poluuid |
707a0d88-c972-51e7-bbc7-4d421660557b |
|
| ☑ | profile |
profile |
g-default |
|
| ☑ | proto |
proto |
6 |
|
| ☑ | qclass |
qclass |
(n/a) | |
| ☑ | qtype |
qtype |
(n/a) | |
| ☑ | quarskip |
quarskip |
File-was-not-quarantined. |
|
| ☑ | radioband |
radioband |
(n/a) | |
| ☑ | rcvdbyte |
rcvdbyte |
39898 |
|
| ☑ | rcvdpkt |
rcvdpkt |
37 |
|
| ☑ | reason |
reason |
malformed input |
|
| ☑ | reqtype |
reqtype |
direct |
|
| ☑ | result |
result |
(n/a) | |
| ☑ | role |
role |
(n/a) | |
| ☑ | security |
security |
(n/a) | |
| ☑ | service |
service |
HTTP |
|
| ☑ | sentbyte |
sentbyte |
1850 |
|
| ☑ | sentpkt |
sentpkt |
25 |
|
| ☑ | sessionid |
sessionid |
8058 |
|
| ☑ | severity |
fortigate_severity |
(n/a) | |
| ☑ | sndetected |
sndetected |
(n/a) | |
| ☑ | srccountry |
srccountry |
Reserved |
|
| ☑ | srcintf |
srcintf |
port12 |
|
| ☑ | srcintfrole |
srcintfrole |
undefined |
|
| ☑ | srcmac |
srcmac |
a2:e9:00:ec:40:01 |
|
| ☑ | srcname |
srcname |
pc1 |
|
| ☑ | srcserver |
srcserver |
0 |
|
| ☑ | service |
service |
HTTPS |
|
| ☑ | ssid |
ssid |
(n/a) | |
| ☑ | stamac |
stamac |
(n/a) | |
| ☑ | status |
status |
success |
|
| ☑ | subtype |
subtype |
forward |
|
| ☑ | trandisp |
trandisp |
snat |
|
| ☑ | transip |
transip |
172.16.200.2 |
|
| ☑ | transport |
trandisp |
40772 |
|
| ☑ | type |
fortigate_type |
traffic |
|
| ☑ | ui |
ui |
(n/a) | |
| ☑ | user |
user |
bob |
|
| ☑ | utmaction |
utmaction |
allow |
|
| ☑ | utmref |
utmref |
0-220586 |
|
| ☑ | vcluster_state |
vcluster_state |
(n/a) | |
| ☑ | vd |
vd |
vdom1 |
|
| ☑ | virus |
virus |
EICAR_TEST_FILE |
|
| ☑ | vpntunnel |
vpntunnel |
(n/a) | |
| ☑ | xauthgroup |
xauthgroup |
(n/a) | |
| ☑ | xauthuser |
xauthuser |
(n/a) |
High-Cardinality (HC) Tags
SrcIPDstIP
Example Logs
Block SSL Traffic
action="blocked" dstintf="unknown-0" dstintfrole="undefined"
dstip="172.16.200.99" dstport="8080" eventtype="ssl-anomalies"
level="warning" logid="1700062053" msg="Connection is blocked due
to unsupported SSL traffic" policyid="1"
profile="block-unsupported-ssl" proto="6" reason="malformed input"
service="SMTPS" sessionid="11424" srcintf="port2"
srcintfrole="undefined" srcip="10.1.100.66" srcport="41296"
subtype="ssl" type="utm" vd="vdom1"
Successful Authentication
date=2019-05-13 time=15:55:56 logid="0102043008" type="event"
subtype="user" level="notice" vd="root" eventtime=1557788156913809277
logdesc="Authentication success" srcip=10.1.100.11 dstip=172.16.200.55
policyid=1 interface="port10" user="bob" group="local-group1"
authproto="TELNET(10.1.100.11)" action="authentication"
status="success" reason="N/A" msg="User bob succeeded in
authentication"
Web Access Denied
date=2019-05-13 time=16:29:45 logid="0316013056" type="utm"
subtype="webfilter" eventtype="ftgd_blk" level="warning" vd="vdom1"
eventtime=1557790184975119738 policyid=1 sessionid=381780
srcip=10.1.100.11 srcport=44258 srcintf="port12"
srcintfrole="undefined" dstip=185.244.31.158 dstport=80
dstintf="port11" dstintfrole="undefined" proto=6 service="HTTP"
hostname="morrishittu.ddns.net" profile="test-webfilter"
action="blocked" reqtype="direct" url="/" sentbyte=84 rcvdbyte=0
direction="outgoing" msg="URL belongs to a denied category in policy"
method="domain" cat=26 catdesc="Malicious Websites" crscore=30
craction=4194304 crlevel="high"
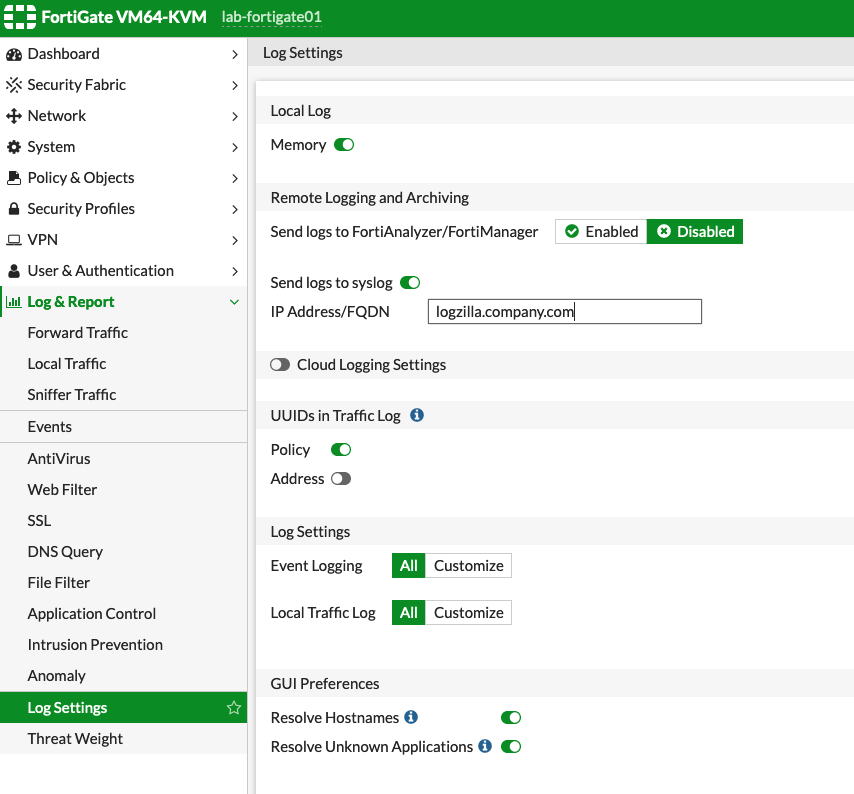
Fortigate Configuration
Fortigate should be configured as follows - Note that Local Traffic Log must be enabled.